How to register on Huulk?
If you want to use it, you should register first. Please, click the Register tab and do the following:
- Fill in your email address.
- Create a password and confirm it.
- It is recommended to use a password you have never used before.
- Click on Register.
- Verify your email address.
- Approve new device.
How to verify my email?
Your e-mail address will be used for confirmations and important notifications. That is why it should be confirmed as soon as possible. We have sent a verification email to your email address. To confirm your email, please do the following:
- Open your inbox and find the e-mail. It should be delivered within 30 minutes. If you can't find it, please check your spam folder.
- Open the e-mail
- Click the button Verify my email address.
- The link will automatically redirect you back to Huulk.com
- Then click the button Log in.
Should you have any issues with the e-mail verification, please contact our support.
How to approve a new device?
This is a process that protects the security of your account. Note that you need to access this email with the same device that you want to have approved.
- Open inbox of your registration email.
- Click the confirmation email we have sent to you.
- Then click the button Approve new device.
- The link will automatically redirect you back to Huulk.
How many accounts can I have?
A single individual may only have one account with Huulk.
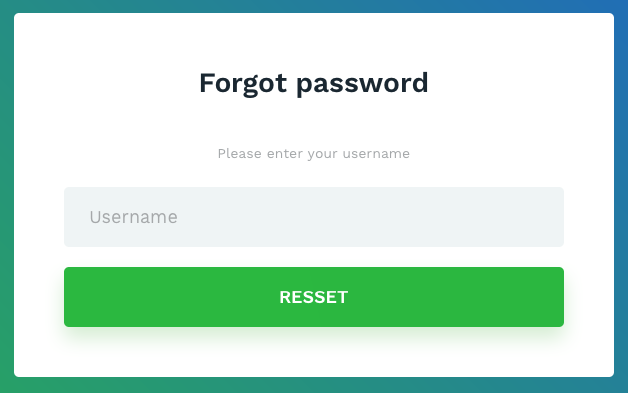
What should I do if I forgot my password?
This is a process that protects the security of your account. If you forgot your password, please do the following:
- Please go to [Home] - [Login] and click [Forgot password].
- Enter the email address that you registered with and open your email inbox.
- Click the reset password link in the email.
- Type and re-enter the new password.
- Click [Set password] to submit.
SMS Authentication
Besides Google 2FA, SMS (short message service) authentication is also an important setting for your account security. Compared with Google 2FA, SMS has less steps to conclude.
SMS authentication consists of four steps:
- Choose the registration country of your phone number.
- Enter your phone number
- Then click the ‘‘Submit” button
- Get your SMS code and enter it into the input box.
The SMS authentication will be successfully bound to your account if all above mentioned information are correct and accurate.
What is Google 2FA?
Google 2FA is an important way for security verification, which is in coordination conducted by the web-end and the mobile-end. The “Security” page in the security center provides two ways of authentication: 2FA (Google Authentication) and SMS (Phone Authentication). You can enable either of them. Here we give 2FA (Google Authentication) as an example.
Steps of Google 2FA are as following:
-
Download the app “Authentication”. IOS users can download this app from the APP Store and users with Android devices can download it from their application stores.
-
Open the app “Authentication”, click “+” at upper right corner, choose ‘‘scan barcode” and open the scanning frame.
-
Use the camera to scan the QR code provided by Huulk.
-
Check your 6-digit pin corresponding to your Huulk account in your cellphone end and enter it into the input field. Now your account is connected to Google 2FA.
How to disable Google 2FA?
- Please log in to Huulk, go to My profile and then find Security login options.
- Click “Disable” in Google Auth section.
- You can disable each category except for the Email. Email verification is required.
What to do if I couldn’t receive any email from Huulk?
If you couldn’t find the email from Huulk, please check your trash mailbox first.
If you could not receive any email from Huulk, please make sure our domain “*.huulk.com” has been added into your email setting as a whitelist address.
(The process of adding a whitelist is in the “Email Settings” -> “Anti-Spam” -> “Whitelist” section, click on the “set whitelist mail address”)
You can also check the list of your blocked addresses. You can find it in your email settings.
What should I do in case I lose my 2FA device and cannot login?
....
Universal 2nd Factor
Universal 2nd Factor (U2F) is an open authentication standard that strengthens and simplifies two-factor authentication (2FA) using specialized USB or NFC devices based on similar security technology found in smart cards.
The USB devices communicate with the host computer using the HID protocol, essentially mimicking a keyboard. This avoids the need for the user to install special hardware driver software in the host computer, and permits application software (such as a browser) to directly access the security features of the device without user effort other than possessing and inserting the device. Once communication is established, the application exercises a challenge–response authentication with the device using public-key cryptography methods and a secret unique device key manufactured into the device. The device key is secured against duplication by a degree of social trust in the commercial manufacturer, and logically secured against reverse-engineering or counterfeiting by the robustness of the encryption and physical possession.
See below, some examples of U2F devices:
- Yubikey
- Trezor Model T
How to use Yubikey.
The YubiKey is a hardware authentication device manufactured by Yubico which supports one-time passwords, public-key encryption and authentication, and the Universal 2nd Factor (U2F) protocol.
- Insert your Yubikey device into the USB port, wait until it has been installed
- Once you plug in the YubiKey, the LED on the device should light up
- Press the gold button for one second – the code from the YubiKey will be automatically entered in the selected field
How to set up your trezor?
The Trezor Model T is the cryptocurrency hardware wallet designed to be a vault for Capricoin. Users can safely store their Capricoins, passwords and other digital keys via this device. Trezor Model T also supports more than 500 coins. .
The Model T can also serve as an U2F hardware token using its screen to inform users about the request for authentication before they will be approved. In this way, Trezor Model T protects users twice from various kinds of cyber-attacks. It offers an intuitive and convenient interface.
The Model T belongs to the most secure vaults using a 4-digit PIN code on its touch-screen. The PIN code and the passphrase are entered exclusively on the device’ touch-screen, hence any communication with the hosting computer is disabled until the correct PIN code is entered. Any operations with private and public keys are allowed only after a successful user authentication via PIN code. This makes the hardware wallet even more secure.
In case you ever lose your device, you can directly recover your entire wallet by using the 12-word recovery seed. Passwords are never stored or remembered on the device and they are individually locked and encrypted with the Trezor Password Manager.
You can find more information here: https://trezor.io/
You can find short and easy tutorial about how to set up your trezor here: Trezor Model T tutorial
